Most Windows management tools behave pretty well with User Account Control (UAC), at least they prompt you for your credentials before actually launching. In the past I already described some of the naughtiness of UAC: Explaining UAC related behavior One of the things that has been bothering me ever since I first met UAC is how the file browser (Windows Explorer) handles UAC.
The problem(s)
One of the dirty things it does for you is adding your account to the ACL of files you normally have access if you are member of the local administrators. This is the prompt you can click continue o-so-easy:
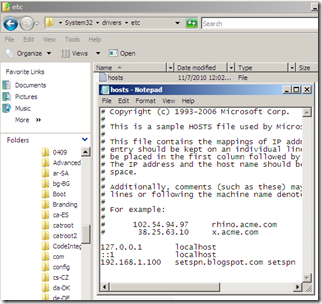
At first sight you’ll be satisfied, after clicking continue and providing your credentials you will see the files & folders. But below the hood your account just got granted access. This doesn’t breaks things, but it’s not nice. The second issue I encounter a lot is when trying to edit a configuration file for an application or service. Or even a easier example: adding an entry to the hosts file. You browse to c:\windows\system32\drivers\etc double click hosts, make your modification and when trying to save…
And after clicking OK you are prompted for a filename and location. Now that’s a lot of hassle to add something to the hosts file.
The workaround:
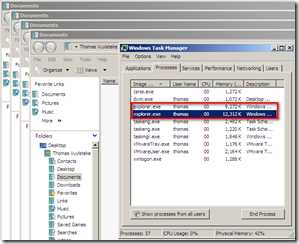
UAC elevation allows you to start a given application (process) in an other context with your elevated token (where you do have administrator privileges). And that’s where things go wrong with Windows Explorer. Out of the box when a user logs on, one instance of explorer.exe is started and all subsequent instances are running from this instance. As the explorer starts with your limited token (non administrator privileges), all other instances are limited as well.
Below you see multiple explorers open, but only one explorer.exe is listed.
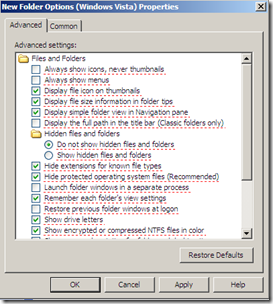
Now there is a modification we can do to alter the behavior of Windows Explorer. We can check “Launch folder windows in a separate process” in the Folder and Search Options.
Whenever we now start multiple Windows Explorer instances, they will all open below the second explorer.exe instance:
This is actually quit remarkable and very subtitle: after setting this option, the first Windows Explorer instance you open, determines under which token the following instances will run.
Automating the workaround:
The “Launch folder windows in a separate process” is a per user setting, and is stored in HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\Advanced as the value SeparateProcess.
But since we have those almighty cool Group Policy Preferences, we can click this setting together in no time:
1. Create a GPO, or alter an existing one and create a new “Folder Options (Windows Vista) below User Configuration > Preferences > Control Panel Settings > Folder Options
2. At first all settings will be underlined in green, meaning all these will be pushed to the user as listed. We can actually alter this behavior with the F5-F6-F7-F8 keys.
3. Press F8 so all settings are underlined in red: none will be applied to the user
4. Check “Launch folder windows in a separate process” and press F6 to underline that specific setting in green so it will be pushed to the user.
Testing the workaround
The easiest way to start Windows Explorer in elevated mode is to locate in in your start menu below Accessories (or type a part of the name in your start menu) and right click and choose Run As Administrator.
After editing something like the hosts file, you’ll be able to save it without prompts:
Whether you set the setting by hand or by GPO, it’s immediately effective. But as the first instance determines the context, you’ll have to close all open Windows Explorer instances first before you can run Windows Explorer as Administrator. This does not include the explorer.exe process which is started immediately at logon. A lot of workarounds for UAC and Windows Explorer explain how to kill the explorer.exe process and relaunch it from an elevated task manager, but in this case there’s no need to do that.
In my opinion this a rather nice workaround. You still have to elevate the Windows Explorer application yourself. The disadvantage is that everything you launch from within that instance is instantly elevated which defeats the purpose of UAC a bit. But then again, this is nothing different from a command prompt you start as an administrator. In both cases administrators should be aware of the risks which launching items from within elevated processes, be it a command prompt or a Windows Explorer instance.
Some additional information: KB2273047 (User Account Control (UAC) and Windows Explorer)
And my UAC settings are those as described in the Enterprise Client security model ( http://technet.microsoft.com/nl-be/bb679962(en-us).aspx –> Table A30. Security Option Setting Recommendations - User Account Control)
Happy elevating,
Thomas.















3 Response to Using Windows Explorer together with UAC
Great post, thanks for the nice write up with images.
I'm still getting my feet wet with GPO preferences.
Also wanted to say this is one of the nicest blogspot theme's I've seen.
Thanks for the thumbs up.
I've just stumbled upon this theme in the blogspot theme galeries. Perhaps I customized it a bit, but credits to the original creator of the theme.
This does not work for 2008 R2
Add Your Comment