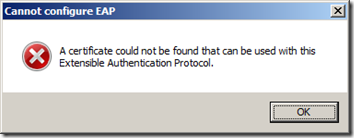
A colleague of mine was trying to configure the NPS (Network Policy Server) role on two Windows 2008 R2 servers (domain controllers) in order to allow the wireless clients to be authenticated. One of the requirements for Protected EAP is a certificate on the server hosting the NPS role. He told me has was seeing a certificate in the personal store of the computer, but he kept receiving the following error: Cannot configure EAP: A certificate could not be found that can be used with this Extensible Authentication Protocol. when trying to select a certificate.
We found out that the NPS role doesn’t like the new Domain Controller Authentication certificate which is supposed to be more or less equivalent to the domain controller certificate from the past.
I’ve configured this a few times in the past, and whenever we were combining the NPS role with a DC I always used the “domain controller” certificate present on the DC. This works just fine. If nobody changed the default auto-enrollment settings in the domain, they should look like this:
A Windows 2008 R2, Enterprise Certificate Authority will have the following templates published by default, I highlighted the relevant ones for Active Directory: Domain Controller, Domain Controller Authentication and Directory Email Replication.
This was different for Standard SKU Windows 2008/2003 Enterprise CA’s, they only had the “domain controller” certificate listed. This was because standard SKU’s couldn’t use V2/V3 templates. You can see the difference in versioning between these templates in the template management mmc. Smaller than 100 means it’s a V1 template:
Here is how the local certificate store of a domain controllers looks like when no auto-enrollment options are configured:
As you can see there’s only one certificate available based on the Domain Controller template. Even without autoenrollment configured a domain controller will try to enroll for such a certificate. This is hardcoded in the domain controller. Just like an EFS client will try to retrieve an EFS certificate. My colleague wasn’t having one certificate though, he was seeing two:
The reason these were enrolled is because auto-enrollment was configured like this:
The checkbox “Update certificates that use certificate templates” enables autoenrollment for issuance of certificates that supersede issued certificates (TechNet: Configure Certificate Autoenrollment). Because both the Domain Controller Authentication and Directory Email Replication templates are configured to supersede the domain controller certificate, a domain controller will no longer have a certificate based on the domain controller template.
The requirements for an EAP certificate are specified in KB814394: Certificate requirements when you use EAP-TLS or PEAP with EAP-TLS. The reason the NPS console doesn’t seems to accept it, is because the Subject is left empty in the Domain Controller Authentication certificate:
I have no idea why they did this, my guess is that they duplicated the domain controller template and forgot to set it. It can be easily set to the domain controller name in a duplicated template:
My advise would be to create a custom template for the NPS servers. This way you can ensure your NPS configuration never becomes invalid because the domain controller certificate is replaced.
P.S. When testing auto enrollment, make sure to execute a gpupdate /force, a gpupdate without the /force doesn’t seem to trigger the auto enrollment process.
Thomas
















8 Response to Error Selecting A Certificate When Configuring NPS
great!!! you saved my day (and weekend)
THANKS!!!!
great ^^
same problem with IAS on Server 2003 an a 2008 R2 CA.
Thanx very much !
My scenario is my CA server is w2k3, AD and NTP w2k8 r2.. it´s no works..!
This is just the issue we experienced in our network. I actually used this to guide Microsoft Product Support to fix the issue for good! Thanks for sharing this!!!!
Thank you!
Does that mean that I only have to change the subject name format from none to like "DNS"?
It's been a while, but yes, if you take DNS it should add dc.contoso.com to the subject and make NPS happy.
Thank You. Saved our bacon
Add Your Comment