Since Windows 2008 there is a new well-known security principal called “Owner Rights”. In the past there were some scenario’s in a delegation situation which could be hard to solve. The following example is specific to Active Directory, but the same principle goes for file permissions.
One problem was the delegation of creating objects without being able to delete them. As the creator is also the owner of the object, he is able to alter the permissions of the object. Another was the situation in which someone gets removed from the groups granting permissions. Because that person originally created the objects and is in fact still listed as owner, he still can also change permissions. In both cases the original creator of the object is capable of granting him or herself full permissions on the objects. Below an example.
The following command allows the group “DL_GroupAdmins” to create groups in the groups OU.
- dsacls "ou=groups,ou=corp,dc=home,dc=local" /I:T /G "home\DL_GroupAdmins":CC;group
After creating a DL_Test group as a member of DL_GroupAdmins, we can clearly see our permissions are very limited (create group objects) and our user “deleg” is listed as owner:
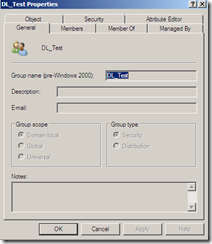
Because our user is listed as owner of the group, he can change permissions to grant himself full control on the object. On the left is a picture showing he can control security, on the right is a screenshot of the general tab after giving himself full control.
And this is where “owner rights” comes in handy. Because the owner can always change permissions, we will redefine what an owner of an object can do. With the following command we will ensure owners of objects will only have generic read permissions.
- dsacls "ou=groups,ou=corp,dc=home,dc=local" /I:T /G "Owner Rights":GR
In my opinion a must: it is really easy to implement and it ensures permissions aren’t being tampered with.










No Response to "Owner Rights"
Add Your Comment